Cybersecurity & Privacy
All social and economic aspects of our lives are shifted every day toward the digitization journey. In this world of constant evolution and transformation, security is the one pillar that provides strong foundation for organizations. Cybersecurity is a constantly evolving landscape, where compliance, security, privacy and business resilience requirements are continuously increasing, as the relevant threats are becoming more and more sophisticated and persistent, making it hard to defend and even harder to predict.

What we deliver
At Uni Systems, we address security challenges through a holistic and integrated approach with an extended range of Cybersecurity and Privacy Services and tools that can provide the expertise needed to overcome even the hardest of those challenges.
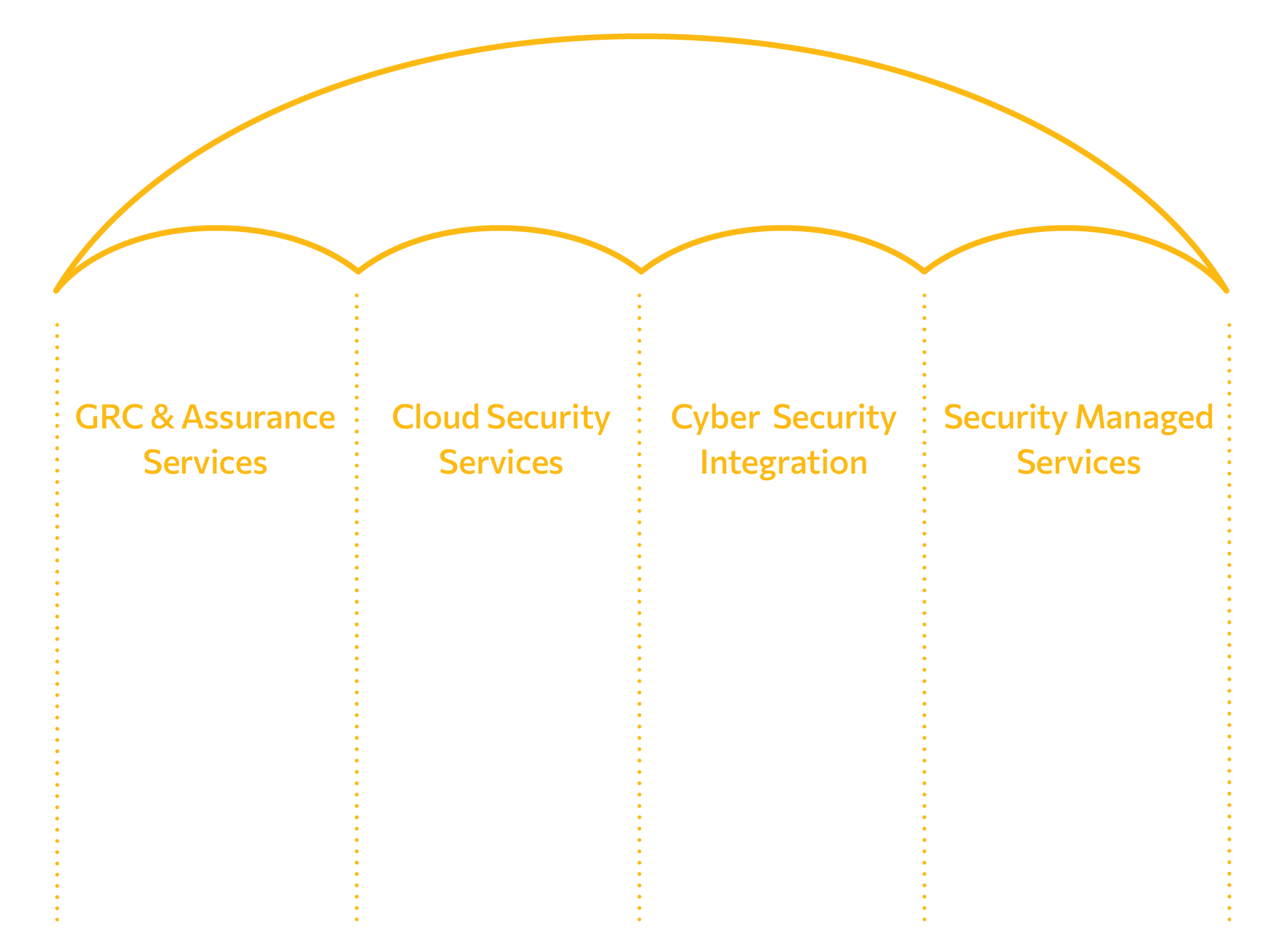
Our Services
Projects
Reference Engagement
Providing a single pane of glass in Endpoint Detection and Response for Critical Infrastructure / Energy Sector
Turn-key migration of multiple endpoint protection platforms to a unified EPP/EDR platform.
Securing Cloud networking infrastructure for the Banking Sector
Integration of Next-Generation Firewall in the form of NVA within the Azure Public Cloud infrastructure.
Supporting the Agency’s mission of improving European Member States.
Penetration Testing of various internal applications and infrastructure.
Proactively discovering vulnerabilities for the Public.
Penetration Testing of public authority’s critical public web applications.
Providing a secure path for improving European Authority’s infrastructure.
Assessment to review the organization’s existing Security Infrastructure, market research, design of new security modern infrastructure.
Assisting in Information Security compliance for the European Authority.
IT security risk assessments of different systems using ITSRM2 and draft the corresponding IT Security Plans.
Advising for the European Authority in matters of risks and planning for new systems.
Execution of risk assessment for new systems and security assurance around technical compliance.
Providing a secure way of sensitive information transfer over the European Union.
Risk assessment and IT Security Plan for the transfer of sensitive documents.
Provision of end-to-end, fully managed Security Services for the European Authority.
Managed Services around Information Security Engineering and Consulting
